A friend of mine recently asked the question on how he could edit the Modern Authentication settings in Office365. He found that when he went to the new Settings Pane for Modern Authentication he could change settings specifically to block older clients.
If you don’t know where to find this, check it out in your Office365 Portal by going to Settings -> Org Settings -> Modern Authentication;
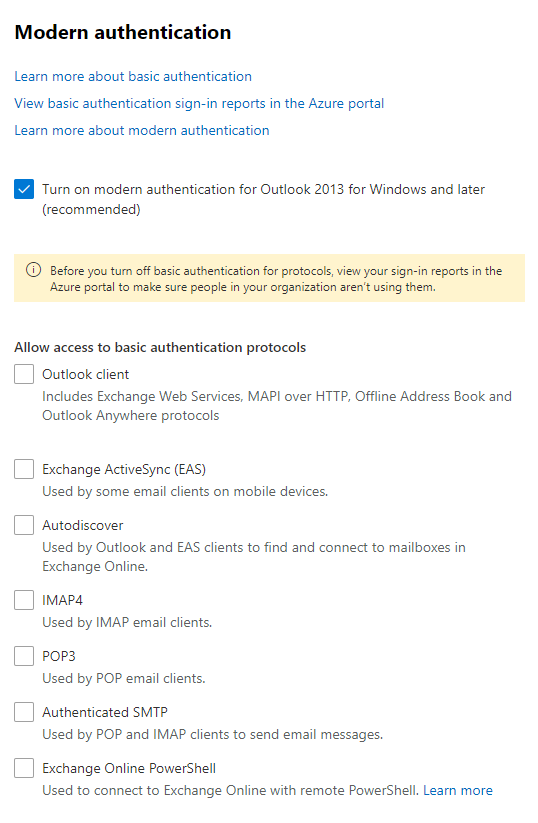
His question was how he could centrally manage these checkboxes. I explained to him that these checkboxes are actually based on something that’s existed for ages; Exchange Authentication policies. It turns out that when you change these settings a new policy is created called “No Basic Auth” and this is set as the default for the entire tenant.
So to centrally manage this it’s actually straight forward – We create our own policy called “No Basic Auth” and enable this as the default policy. From the moment this policy is deployed you’ll also be able to change these settings via the portal and they will be reflected immediately. So let’s get to the script.
This script disables all forms of basic authentication for you, so it copies the screenshot above. It’s a good plan to slowly start implementing this at all your clients – In just 6 months basic authentication is being completely deprecated with no way to turn it back on. Doing this now allows you and your clients to prepare.
The Script
######### Secrets #########
$ApplicationId = 'AppID'
$ApplicationSecret = 'AppSecret' | ConvertTo-SecureString -Force -AsPlainText
$TenantID = 'TenantID'
$RefreshToken = 'VeryLongReFreshToken'
$ExchangeRefreshToken = 'ExchangeRefreshToken'
$UPN = "UPNUSedToGenerateTokens"
######### Secrets #########
$credential = New-Object System.Management.Automation.PSCredential($ApplicationId, $ApplicationSecret)
$aadGraphToken = New-PartnerAccessToken -ApplicationId $ApplicationId -Credential $credential -RefreshToken $refreshToken -Scopes 'https://graph.windows.net/.default' -ServicePrincipal -Tenant $tenantID
$graphToken = New-PartnerAccessToken -ApplicationId $ApplicationId -Credential $credential -RefreshToken $refreshToken -Scopes 'https://graph.microsoft.com/.default' -ServicePrincipal -Tenant $tenantID
Connect-MsolService -AdGraphAccessToken $aadGraphToken.AccessToken -MsGraphAccessToken $graphToken.AccessToken
$CurrentConf = $customers = Get-MsolPartnerContract -All
foreach ($customer in $customers) {
write-host " Processing $($customer.DefaultDomainName)"
$token = New-PartnerAccessToken -ApplicationId 'a0c73c16-a7e3-4564-9a95-2bdf47383716'-RefreshToken $ExchangeRefreshToken -Scopes 'https://outlook.office365.com/.default' -Tenant $customer.TenantId
$tokenValue = ConvertTo-SecureString "Bearer $($token.AccessToken)" -AsPlainText -Force
$credential = New-Object System.Management.Automation.PSCredential($upn, $tokenValue)
$customerId = $customer.DefaultDomainName
$session = New-PSSession -ConfigurationName Microsoft.Exchange -ConnectionUri "https://ps.outlook.com/powershell-liveid?DelegatedOrg=$($customerId)&BasicAuthToOAuthConversion=true" -Credential $credential -Authentication Basic -AllowRedirection
$null = Import-PSSession $session -AllowClobber -CommandName "Set-AuthenticationPolicy", "Get-AuthenticationPolicy", "Get-OrganizationConfig", "New-AuthenticationPolicy", "Get-OrganizationConfig", "set-OrganizationConfig"
$null = New-AuthenticationPolicy -Name "No Basic Auth" -AllowBasicAuthActiveSync:$FALSE -AllowBasicAuthAutodiscover:$FALSE -AllowBasicAuthImap:$false -AllowBasicAuthMapi:$FALSE -AllowBasicAuthOfflineAddressBook:$FALSE -AllowBasicAuthOutlookService:$FALSE -AllowBasicAuthPop:$FALSE -AllowBasicAuthPowershell:$FALSE -AllowBasicAuthReportingWebServices:$FALSE -AllowBasicAuthRpc:$FALSE -AllowBasicAuthSmtp -AllowBasicAuthWebServices:$FALSE -erroraction silentlycontinue
$null = Set-OrganizationConfig -DefaultAuthenticationPolicy "No Basic Auth"
Remove-PSSession $session
}
And that’s it! As always, Happy PowerShelling!