I’ve been trying to explore how Microsoft generates MFA pushes for some time now. I wanted to offer the same functionality for tools I am building. One of them being a AAD RADIUS replacement tool that’s almost done for public use, the other is a method of verifying the identity of a specific user. Unfortunately Microsoft doesn’t really publish any documentation about how they generate these tokens and send them to users.
After some reverge engineering and checking how the tokens are both received and sent on devices I’ve been able to create a PowerShell script that allows you to send MFA requests to any user that you administer either in your own tenant, or in client tenants using the secure application model. As an example I’ve included a user validation portal Azure Function, but of course you can use this in any process where you need to confirm that the user is really themselves.
Example Azure Function
Click the deploy button below to create the Azure Function that allows you send MFA requests to any user in your tenant.
 After clicking the button and entering your Secure Application Model IDs and deploying the application, visiting the application will present you with this screen, enter a username there and press send and it’ll send the MFA request to a user, allowing you to validate their identity. This only works with push-based MFA types, such the PhoneApp, passwordless, or a phone call.
After clicking the button and entering your Secure Application Model IDs and deploying the application, visiting the application will present you with this screen, enter a username there and press send and it’ll send the MFA request to a user, allowing you to validate their identity. This only works with push-based MFA types, such the PhoneApp, passwordless, or a phone call.
Example Script
The GenPass should be a generated password. The first time you execute this for a tenant it might fail as it takes some time for the password to apply to the application in your M365 environment.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
|
######### Secrets #########
$ApplicationId = 'ApplicationID'
$ApplicationSecret = 'ApplicationSecret'
$RefreshToken = 'RefreshToken'
$EmailToPush = "Youruser@receivepush.com"
$Genpass = 'RandomGeneratedPasswordToSetOnMFAApplicationPleaseKeepThisSecureAsItCanBeUsedToGenerateMFARequests'
######### Secrets #########
write-host "Creating credentials and tokens." -ForegroundColor Green
$credential = New-Object System.Management.Automation.PSCredential($ApplicationId, ($ApplicationSecret | Convertto-SecureString -AsPlainText -Force))
$aadGraphToken = New-PartnerAccessToken -ApplicationId $ApplicationId -Credential $credential -RefreshToken $refreshToken -Scopes 'https://graph.windows.net/.default' -ServicePrincipal
$graphToken = New-PartnerAccessToken -ApplicationId $ApplicationId -Credential $credential -RefreshToken $refreshToken -Scopes 'https://graph.microsoft.com/.default' -ServicePrincipal
write-host "Connecting to MSOL" -ForegroundColor Green
Connect-MsolService -AdGraphAccessToken $aadGraphToken.AccessToken -MsGraphAccessToken $graphToken.AccessToken
$UserTenantName = $EmailToPush -split '@' | Select-Object -last 1
$UserTenantGUID = (Invoke-WebRequest "https://login.windows.net/$UserTenantName/.well-known/openid-configuration" | ConvertFrom-Json).token_endpoint.Split('/')[3]
$MFAAppID = '981f26a1-7f43-403b-a875-f8b09b8cd720'
write-host "Setting temporary password" -ForegroundColor Green
New-MsolServicePrincipalCredential -TenantId $UserTenantGUID -AppPrincipalId $MFAAppID -Type password -Usage verify -Value $GenPass -Verbose
write-host "Generating XML" -ForegroundColor Green
$XML = @"
<BeginTwoWayAuthenticationRequest>
<Version>1.0</Version>
<UserPrincipalName>$EmailToPush</UserPrincipalName>
<Lcid>en-us</Lcid><AuthenticationMethodProperties xmlns:a="http://schemas.microsoft.com/2003/10/Serialization/Arrays"><a:KeyValueOfstringstring><a:Key>OverrideVoiceOtp</a:Key><a:Value>false</a:Value></a:KeyValueOfstringstring></AuthenticationMethodProperties><ContextId>69ff05bf-eb61-47f7-a70e-e7d77b6d47d0</ContextId>
<SyncCall>true</SyncCall><RequireUserMatch>true</RequireUserMatch><CallerName>radius</CallerName><CallerIP>UNKNOWN:</CallerIP></BeginTwoWayAuthenticationRequest>
"@
$body = @{
'resource' = 'https://adnotifications.windowsazure.com/StrongAuthenticationService.svc/Connector'
'client_id' = $MFAAppID
'client_secret' = $Genpass
'grant_type' = "client_credentials"
'scope' = "openid"
}
$ClientToken = Invoke-RestMethod -Method post -Uri "https://login.microsoftonline.com/$UserTenantGUID/oauth2/token" -Body $body
$headers = @{ "Authorization" = "Bearer $($ClientToken.access_token)" }
write-host "Generating MFA Request" -ForegroundColor Green
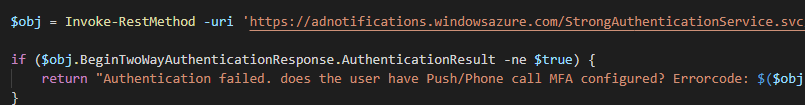
$obj = Invoke-RestMethod -uri 'https://adnotifications.windowsazure.com/StrongAuthenticationService.svc/Connector//BeginTwoWayAuthentication' -Method POST -Headers $Headers -Body $XML -ContentType 'application/xml'
if($obj.BeginTwoWayAuthenticationResponse.AuthenticationResult -ne $true){
write-host "Authentication failed, does the user have Push/Phone call MFA configured?"
}
|
With this you could implement Azure AD based MFA in your own applications, I have some other blogs incoming that will show you how to combine this with an Azure Function to create a RADIUS alternative that supports AAD, and some other cool gizmos. As always, Happy PowerShelling.
After clicking the button and entering your Secure Application Model IDs and deploying the application, visiting the application will present you with this screen, enter a username there and press send and it’ll send the MFA request to a user, allowing you to validate their identity. This only works with push-based MFA types, such the PhoneApp, passwordless, or a phone call.