A friend of mine recently asked if I had a solution for monitoring ADFS and exchange certificates. Funnily this was actually a challenge I’ve struggled with in the past. The problem is that each of these systems has their own way of getting the currently installed certificates.
So when I was playing around creating a list of all commands that we could use to collect the certificates, I remembered an earlier trick I used to check the bindings for SSTP certificates. Using netsh is an easy way to grab all the current bindings, independent of all cmdlets supplied by products directly.
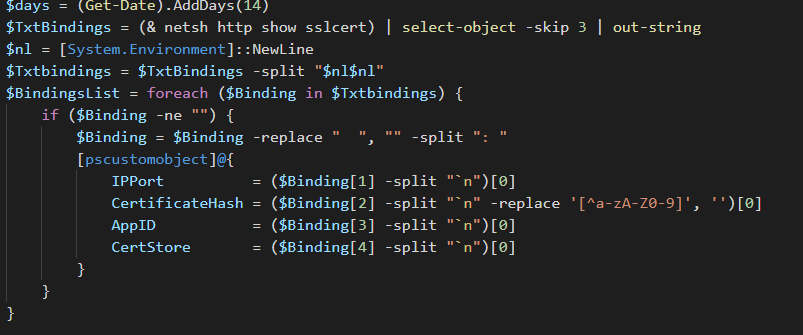
The only problem with the netsh commands that we need to use is that these are not converted to a Powershell native command yet. That means it’s pretty much up to us to play with the strings to get the results we want. Using the script below, you can monitor all the current certificate bindings on a server. Be it Exchange, ADFS, SSTP, or whatever else.
Change the $days variable to how many days before expiry you want to get alerted on.
|
|
You might want to alert on other things, so feel free to customize the script of course. And that’s it. As always, Happy PowerShelling!